Quantum computing is evolving at a blistering pace. While it promises breakthroughs in everything from drug discovery to climate modeling, it also endangers the public-key cryptography that secures virtually every digital interaction today. The hypothetical moment when a sufficiently powerful quantum computer renders current encryption obsolete is known as “Q-Day.” Experts warn that the disruption could eclipse the Y2K scare—unless we act now.
What Is Q-Day and Why Does It Matter?
Q-Day marks the first time a quantum computer can run Shor’s algorithm at the scale needed to break RSA-2048 and other widely deployed schemes. From that point forward, any data protected solely by traditional public-key cryptography—emails, financial records, medical files, classified government traffic—becomes readable to whoever controls or rents such a machine. Unlike Y2K, the risk is not a single calendar bug but a fundamental mathematical vulnerability baked into the internet’s security model.
How Quantum Computers Crack Encryption
Classical encryption relies on problems that are easy to verify but hard to solve, such as factoring large integers (RSA) or computing discrete logarithms (Elliptic-Curve Cryptography). A fault-tolerant quantum computer can solve these problems exponentially faster:
Shor’s Algorithm: Breaks RSA, DSA, and ECDSA by factoring large numbers or solving discrete logs in polynomial time.
Grover’s Algorithm: Halves the effective key length of symmetric ciphers like AES, forcing longer keys but not rendering them useless.
Current best estimates suggest that around 4,000 logical qubits and millions of physical qubits—accounting for error correction—would be needed to threaten RSA-2048. Researchers at IBM, Google, and the Chinese Academy of Sciences are targeting fault-tolerant architectures that could reach that scale within one or two decades, perhaps sooner.
Vulnerable Systems and Potential Fallout
Encryption underpins far more than email and online shopping:
- Finance: SWIFT messages, interbank transfers, and blockchain signatures all rely on RSA or ECDSA.
- Critical Infrastructure: Power grids, water systems, and transportation networks use VPNs and SSL/TLS certificates for remote control.
- Healthcare: Electronic medical records (EMR) and connected devices transmit private patient data.
- Government & Defense: Classified communications and weapons systems depend on public-key cryptography for secrecy and authentication.
If Q-Day arrives before migration to quantum-secure protocols, attackers could retroactively decrypt data already harvested (“store now, decrypt later”) or forge digital signatures to impersonate legitimate entities.
The Race Toward Post-Quantum Cryptography
Post-quantum cryptography (PQC) refers to algorithms believed to resist both classical and quantum attacks while running on today’s hardware. The U.S. National Institute of Standards and Technology (NIST) is finalizing a new suite of standards, including:
- CRYSTALS-Kyber (key encapsulation) and CRYSTALS-Dilithium (digital signatures) based on lattice problems.
- FALCON and Sphincs+ for additional signature diversity.
Implementation, however, is not as simple as a software update. Certificate authorities, network appliances, embedded devices, and long-life IoT sensors must be upgraded—often years before their field replacement.
Obstacles Slowing Global Readiness
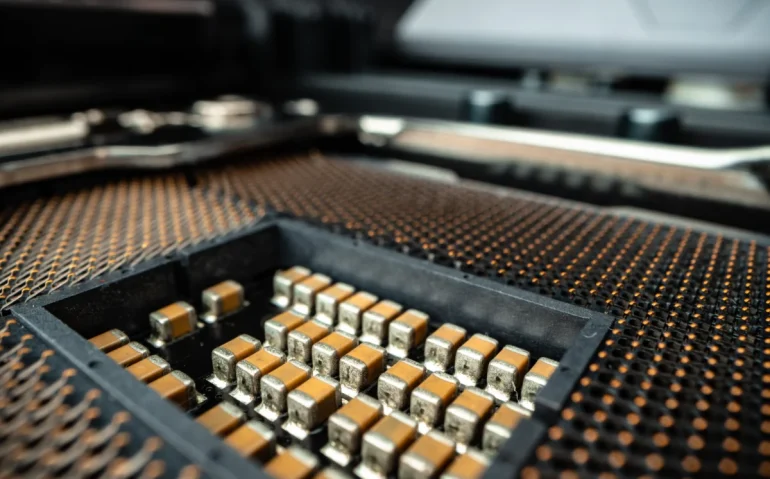
Legacy Hardware: Millions of routers, smart meters, and industrial controllers lack the processing power or memory to run larger PQC keys.
Supply-Chain Timelines: Hardware refresh cycles in critical infrastructure can span 10–30 years.
Standardization Lag: International coordination through bodies like ISO and ETSI takes time, which adversaries may exploit.
Awareness & Funding: Many small- and medium-size enterprises remain unaware of the threat or assume it is only a distant concern.
Strategic Steps for Governments, Businesses, and Individuals
1. Perform a Crypto Inventory. Identify where and how public-key cryptography is used—software libraries, hardware modules, certificates, and data at rest.
2. Adopt a Hybrid Approach. Implement dual-algorithm frameworks (classical + PQC) during the transition, preserving backward compatibility.
3. Prioritize Long-Term Secrets. Protect data that must stay confidential for decades—medical records, state secrets—by moving it to PQC or symmetric-key wrappers today.
4. Harden Symmetric Cryptography. Use AES-256 and SHA-384/512 to mitigate Grover’s algorithm until larger-key post-quantum solutions are ubiquitous.
5. Mandate Vendor Compliance. Incorporate PQC readiness into procurement contracts and software bills of materials (SBOM).
Timeline Estimates: When Could Q-Day Arrive?
Forecasts vary, but consensus ranges from 5 to 20 years for a machine capable of breaking RSA-2048. An unexpected breakthrough in error correction or qubit stability could accelerate this. Conversely, engineering hurdles might push the date further out, but the “harvest now, decrypt later” threat already exists.
Turning the Threat into an Opportunity
The Y2K crisis ended largely uneventfully because organizations responded early, invested in upgrades, and coordinated globally. Q-Day demands the same proactive mindset, with one crucial difference: the fix is not a one-time patch but a permanent shift in our cryptographic foundations. By embracing post-quantum standards, redesigning security architectures, and fostering cross-sector collaboration, we can transform a looming catastrophe into a catalyst for a safer digital future.